Cloud Security and Networking: VPC Isolation
💡 Quick Tip
Key: Your cloud network should be isolated by default. Use public and private subnets to protect your data.
The Concept of VPC (Virtual Private Cloud)
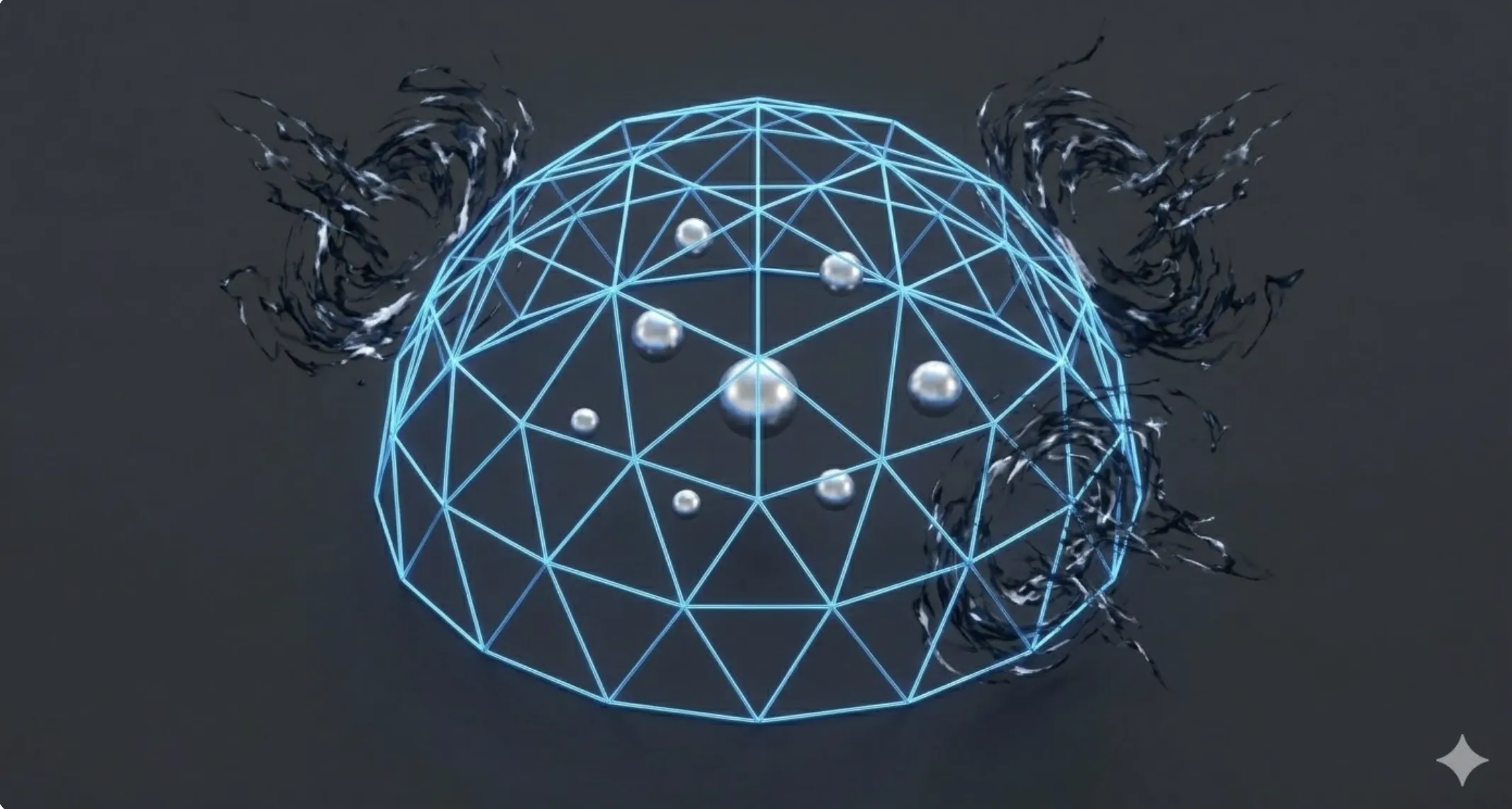
In a cloud environment, servers share physical hardware with thousands of other companies. The technical mechanism ensuring data isolation is the VPC (Virtual Private Cloud). A VPC is a logically isolated section of a cloud provider's network where you define your own IP range, subnets, and route tables.
Public vs. Private Subnets
A secure network architecture divides resources into two zones:
- Public Subnet: Hosts load balancers or web servers accessible from the Internet via an Internet Gateway.
- Private Subnet: Hosts databases and business logic. It has no direct outside access, only communicating with the public subnet. This creates a logical physical barrier against external attacks.
Security Groups and ACLs
Cloud security is multi-layered:
- Security Groups: Act as an instance-level (server) firewall. They are "stateful": allowing an inbound connection automatically allows the outbound response.
- Network ACLs: Act as a subnet-level firewall. They are "stateless" and block malicious IP ranges before they even touch your servers.
📊 Practical Example
Real-World Scenario: Isolating a Customer Database
Step 1: Subnet Creation. We configure a private subnet with no route to the Internet Gateway. We place our SQL database instance there.
Step 2: Security Group Configuration. We create a rule only allowing inbound traffic on port 3306 (MySQL) if it originates specifically from the web server's Security Group.
Step 3: Controlled Egress (NAT Gateway). If the database needs Internet access for security updates, we use a NAT Gateway in the public subnet. It allows outbound-initiated connections, but nobody from outside can initiate one inward.
Step 4: Audit. We use VPC Flow Logs to verify no strange connection attempts. Lacking a public IP, the database is technically invisible to automated Internet scanners.

